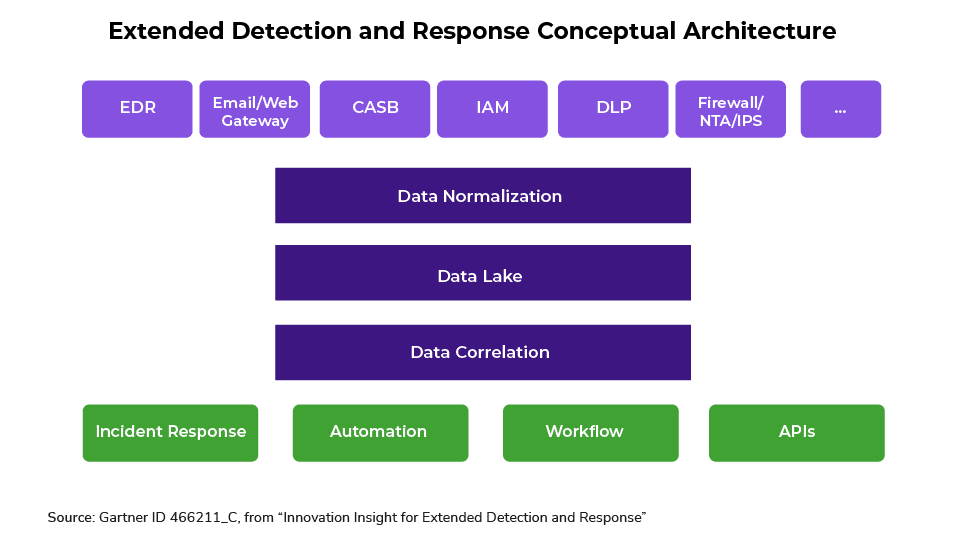
Many cybersecurity solutions operate in siloed technology stacks. Organizations deploy one solution for endpoints, another for cloud workloads, and yet another for the network layer. Aside from being inefficient, this approach also can be highly ineffective—allowing threats to go undetected…
Source: securityboulevard.com – Read more

Critical Claude Code Flaw Silently Bypasses Developer-Configured Security Rules
A high-severity security bypass vulnerability in Anthropic’s Claude Code AI coding agent allows malicious actors to silently evade user-configured deny rules through a simple command-padding