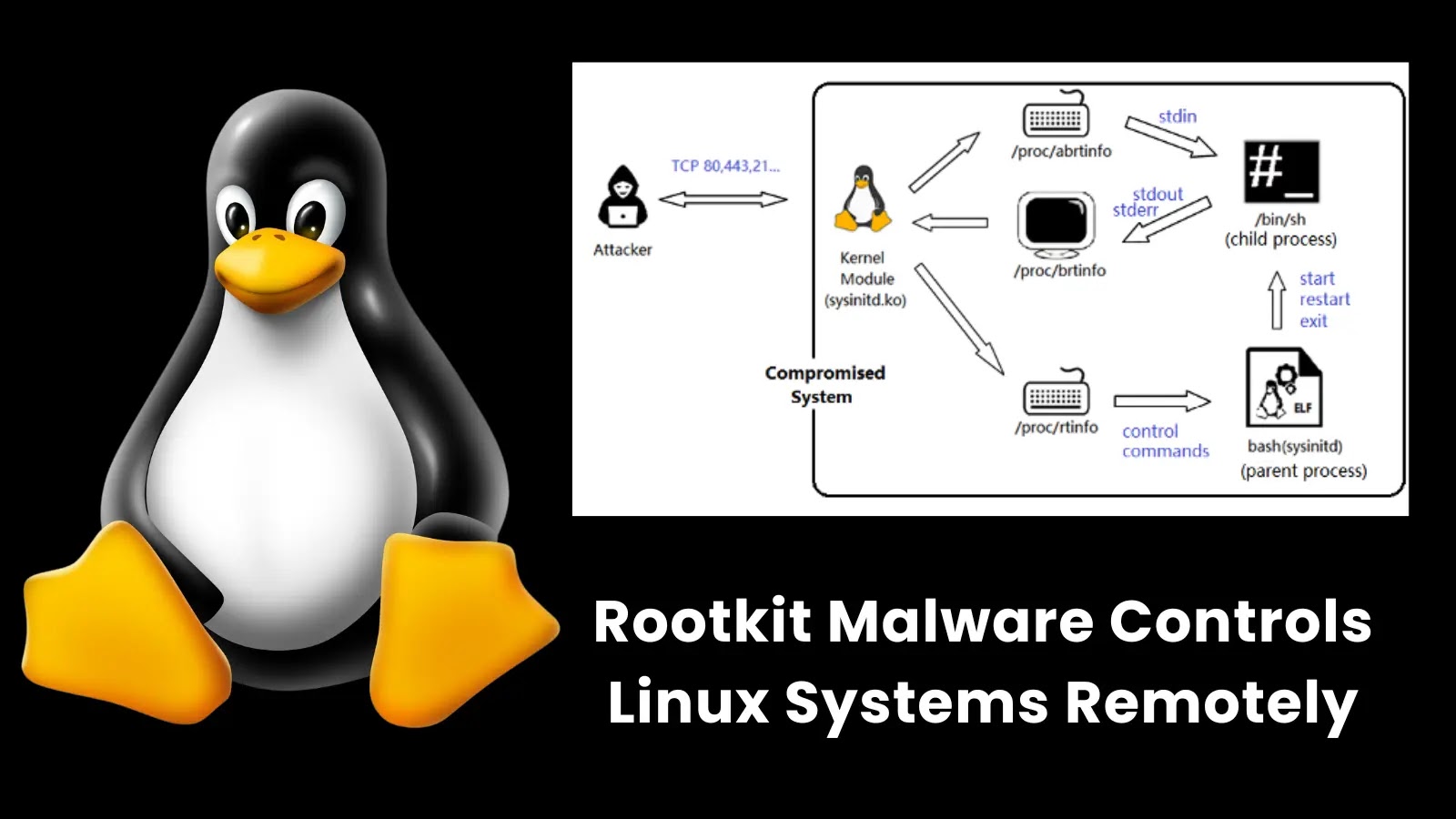
Fortinet has discovered a sophisticated rootkit malware exploiting multiple zero-day flaws in enterprise appliances. The malware uses kernel modules and user-space processes to gain persistence, intercept network traffic, and control compromised Linux-based systems. The malware was embedded in key Linux configuration files to ensure it loaded during system boot. It could execute Linux commands remotely and hijack TCP sessions. Fortinet urged regular updates of systems, monitoring of processes and traffic, and improved security of /proc directory permissions.

U.S. Dismantles DanaBot Malware Network, Charges 16 in $50M Global Cybercrime Operation
The U.S. Department of Justice announced punitive action against 16 individuals accused of developing and using DanaBot malware, controlled by a Russian cybercrime organisation. The