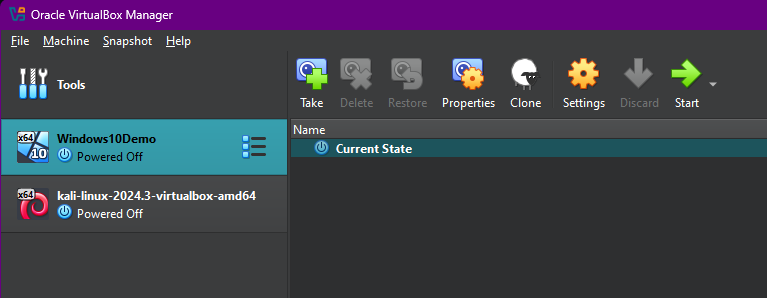
The author explains how to collect data on potential malware attacks on a system using telemetry, and create malware on a virtual machine for learning purposes. They use a Kali virtual machine to attack a Windows machine, utilizing the network discovery tool Nmap to scan the target. The author also uses MSFvenom to develop basic malware, using a handler to listen for network connections from the payload. A HTTP server is set up to facilitate the transfer of the malware between machines in this simulated attack.

The NCSC wants developers to get serious on software security
The NCSC’s new Software Security Code of Practice has been praised by cyber professionals as a significant advancement in enhancing software supply chain security.