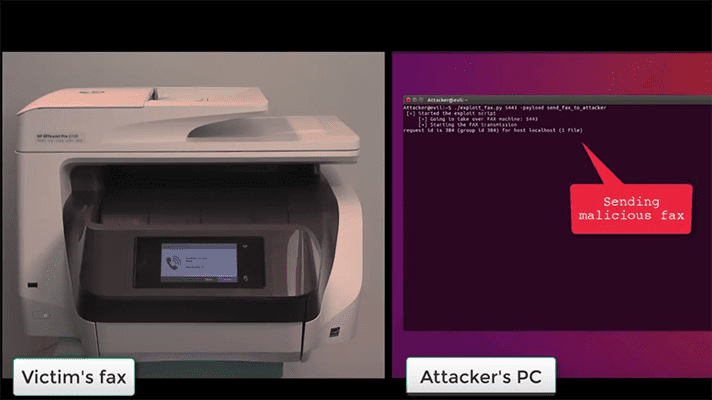
Researchers at Check Point have discovered a vulnerability in the ITU T.30 fax protocol that could be exploited to launch a cyber attack and gain access to a network. Hackers only need a fax number to exploit the flaw, and can then gain remote code execution rights on the device, allowing them to run malicious code and compromise other devices on the network. There are currently no security tools that scan incoming faxes, making prevention of the exploit difficult. Organizations must patch individual fax devices and all-in-one machines to block unauthorized access.

Ingram Micro back online following cyber incident, claims incident is “contained” – CRN Australia
Summarize this content to a maximum of 60 words: Ingram Micro back online following cyber incident, claims incident is “contained” CRN Australia