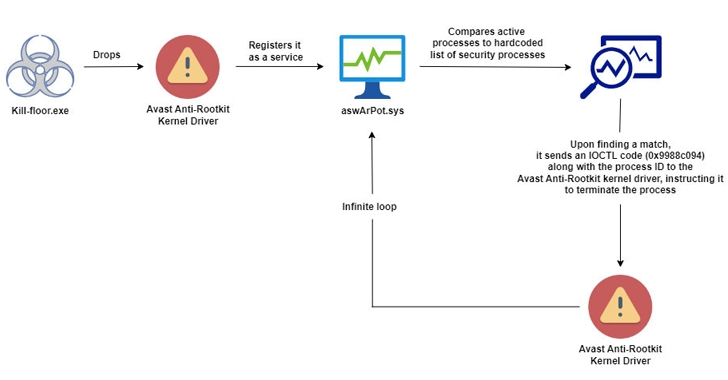
Researchers found a new malware campaign that uses a Bring Your Own Vulnerable Driver (BYOVD) technique. This malware drops a legitimate Avast Anti-Rootkit driver and manipulates it to disable protective software, seize control of the system, and terminate 142 processes, including security software. While the exact access vector and the scope of these attacks aren’t clear, such methods have been widely used to deploy ransomware recently.

Shrinking the IAM Attack Surface through Identity Visibility and Intelligence Platforms (IVIP)
The Fragmented State of Modern Enterprise Identity Enterprise IAM is approaching a breaking point. As organizations scale, identity becomes increasingly fragmented across thousands of applications, decentralized teams,